How To: Configure Your Domain with Windows Live Hotmail
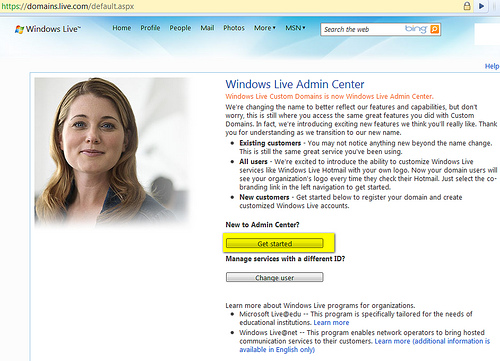
Windows Live Admin Center (changed from Windows Live Custom Domains in November 2007) is a service provided by Windows Live. It enables users with domain names to change their domain MX record (Mail Server) so that they can enjoy the full features of Windows Live Hotmail on their personalized domain.Email accounts provided by Admin Center …